- Home
- Subscribe
- Fusion
-
EBS
- Subscribe EBS Training
- EBS Installation
- EBS Short-Term Consulting
-
EBS Functional Courses
- Fundamentals
- Financials
- SCM
- Supplier Management
-
Procurement
- R12i Oracle Procurement Contracts Fundamentals
- R12i Oracle Sourcing Fundamentals
- R12i Oracle Sourcing - Advanced
- R12i Oracle Purchasing Fundamentals
- R12i Oracle Purchasing - Advanced
- R12i Oracle iProcurement Fundamentals
- R12i Oracle Services Procurement Fundamentals
- R12i Oracle iSupplier Portal Fundamentals
- R12i Oracle Services Procurement Fundamentals - processes for Fixed Priced Contracts
- CRM
- Order Management
- Service
- Grants Management
- Projects
- Discrete Manufacturing
-
EBS Apps DBA Courses
- R11i Oracle E-Business Suite Installation
- R12.2 Install, Patch and Maintain Oracle E-Business Suite
- Oracle E-Business Suite Release 12.2.4 Installation and Patching - End To End
- Oracle E-Business Suite Release 12.2.7 Installation and Patching on Oracle Linux 7.5
- Oracle E-Business Suite Release 12.2 Installation in Cloud Server
- Oracle E-Business Suite Release 12.2.0 to 12.2.5 Upgrade in Cloud Server
- Implementation Method
- Download - Process Flows
- Everything Club
- Pricing
- Interests
- Resources
- Home
- Subscribe
-
Fusion
- Subscribe Fusion Training
- Fusion Cloud Functional Courses
- Fusion Apps DBA Course
- EBS
- Subscribe EBS Training
- EBS Installation
- EBS Short-Term Consulting
-
EBS Functional Courses
- Fundamentals
- Financials
- SCM
- Supplier Management
-
Procurement
- R12i Oracle Procurement Contracts Fundamentals
- R12i Oracle Sourcing Fundamentals
- R12i Oracle Sourcing - Advanced
- R12i Oracle Purchasing Fundamentals
- R12i Oracle Purchasing - Advanced
- R12i Oracle iProcurement Fundamentals
- R12i Oracle Services Procurement Fundamentals
- R12i Oracle iSupplier Portal Fundamentals
- R12i Oracle Services Procurement Fundamentals - processes for Fixed Priced Contracts
- CRM
- Order Management
- Service
- Grants Management
- Projects
- Discrete Manufacturing
-
EBS Apps DBA Courses
- R11i Oracle E-Business Suite Installation
- R12.2 Install, Patch and Maintain Oracle E-Business Suite
- Oracle E-Business Suite Release 12.2.4 Installation and Patching - End To End
- Oracle E-Business Suite Release 12.2.7 Installation and Patching on Oracle Linux 7.5
- Oracle E-Business Suite Release 12.2 Installation in Cloud Server
- Oracle E-Business Suite Release 12.2.0 to 12.2.5 Upgrade in Cloud Server
- Implementation Method
- Download - Process Flows
- Everything Club
- Pricing
- Interests
- Home
- Subscribe
-
Fusion
- Subscribe Fusion Training
- Fusion Cloud Functional Courses
- Fusion Apps DBA Course
- EBS
- Subscribe EBS Training
- EBS Installation
- EBS Short-Term Consulting
-
EBS Functional Courses
- Fundamentals
- Financials
- SCM
- Supplier Management
-
Procurement
- R12i Oracle Procurement Contracts Fundamentals
- R12i Oracle Sourcing Fundamentals
- R12i Oracle Sourcing - Advanced
- R12i Oracle Purchasing Fundamentals
- R12i Oracle Purchasing - Advanced
- R12i Oracle iProcurement Fundamentals
- R12i Oracle Services Procurement Fundamentals
- R12i Oracle iSupplier Portal Fundamentals
- R12i Oracle Services Procurement Fundamentals - processes for Fixed Priced Contracts
- CRM
- Order Management
- Service
- Grants Management
- Projects
- Discrete Manufacturing
-
EBS Apps DBA Courses
- R11i Oracle E-Business Suite Installation
- R12.2 Install, Patch and Maintain Oracle E-Business Suite
- Oracle E-Business Suite Release 12.2.4 Installation and Patching - End To End
- Oracle E-Business Suite Release 12.2.7 Installation and Patching on Oracle Linux 7.5
- Oracle E-Business Suite Release 12.2 Installation in Cloud Server
- Oracle E-Business Suite Release 12.2.0 to 12.2.5 Upgrade in Cloud Server
- Implementation Method
- Download - Process Flows
- Everything Club
- Pricing
- Interests
Hardening RHEL 7.1 (Maipo) - Part 1 - User access
On this document I will go through a series of steps to configure the most relevant settings to harden a RHEL server.
This document is based on the Red Hat Enterprise Linux 7 Security Guide that can be downloaded from the RedHat network here.
Secure passwords
Passwords are the primary method that Red Hat Enterprise Linux 7 uses to verify a user's
identity. This is why password security is so important for protection of the user, the
workstation, and the network.By default RHEL uses shadow passwords which eliminate this type of attack by storing the password hashes in the file /etc/shadow, which is readable only by the root user.
Strong passwords
Since the storing of passwords has already been taken care of the next step is to force the creation of strong passwords.
When users are asked to create or change passwords, they can use the passwd
command-line utility, which is PAM-aware (Pluggable Authentication Modules) and checks to
see if the password is too short or otherwise easy to crack. This checking is performed by
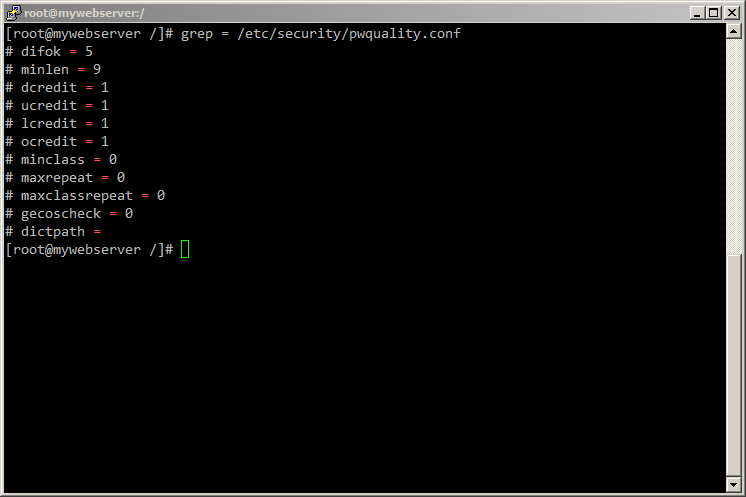
the pam_pwquality.so PAM module.PAM reads its configuration from the /etc/pam.d/passwd file, but the file we want to edit for tuning password policies is /etc/security/pwquality.conf
Have a look at the configuration options:
Here are the details of what each entry means:
- difok - Number of characters in the new password that must not be present in the old password.
- minlen - Minimum acceptable size for the new password
- dcredit - Credit for having digits in the new password
- ucredit - Credit for having uppercase characters in the new password
- lcredit - Credit for having lowercase characters in the new password
- ocredit - Credit for having other characters in the new password
- maxrepeat - maximum number of allowed consecutive same characters in the new password.
- minclass - minimum number of required classes of characters for the new password (digits, uppercase, lowercase, others).
- maxclassrepeat - maximum number of allowed consecutive characters of the same class in the new password.
- gecoscheck - Whether to check for the words from the passwd entry GECOS string of the user (0=check).
- dictpath - Path to the cracklib dictionaries. Blank is to use the cracklib default.
NOTE: Credit works like money, if you have a plus number like three you have spare and don't have to worry, but if you have a negative number (debts) you have to pay for them. For instance "ucredit = 2" means the user will have to give at least two upper case characters as part of the password for creating a password.
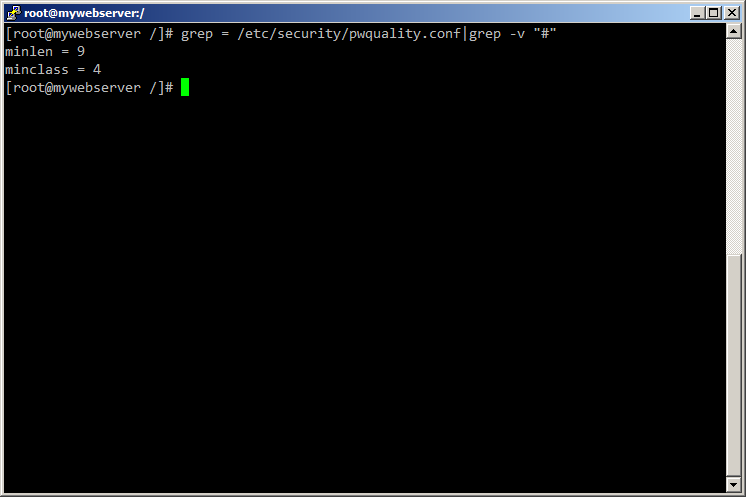
Something practical to do is to set a "minlen = 8" value and "minclass = 4" value. Whith this two settings you would ensure that the password has to be at least 8 characters long and that it will need to have letters Upper case, Lower case, numbers and symbols. That is what you will normally find on production servers.
Some like to uncomment dictpath and let GECOS use the default dictionary. You could go much further with this, but it is not recommended because passwords would need to be too complex and users wouldn't be able to remember them and the SA would have to be resetting passwords too often.
This is the result of a strong password file:
NOTE: As the root user is the one who enforces the rules for password creation, he can set any password for himself or for a regular user, despite the warning messages.
Password aging
This technique is used to limit the time of cracked passwords. The downside is that if you set this value too low (password change required very often) the users will tend to write their passwords down generating a weak spot.
A common practice is to specify the maximum number of days for which the password is valid.
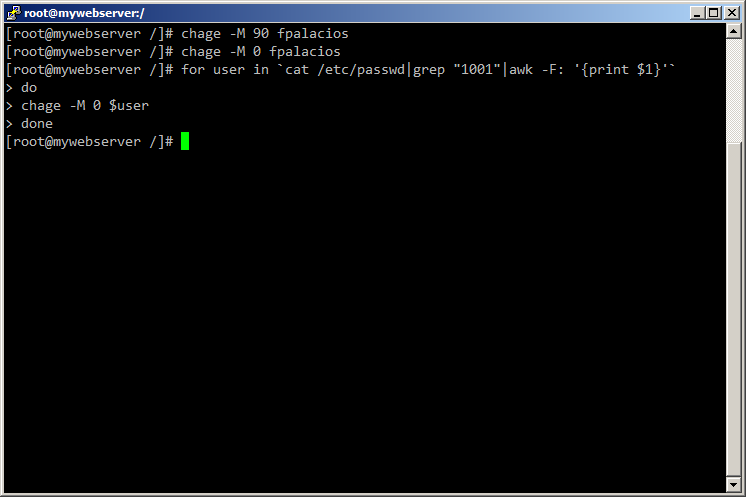
Password aging is performed with the command "chage".
This command is normally used when hardening a system to expire old unsecure password immediately.
I will show three examples on how to use this command on a console.
- Set a 90 day period for the password of user fpalacios to expire.
- Expire the password for fpalacios to have the user change it on the next log on.
- Expire the password of every user on group developers.
Account Locking
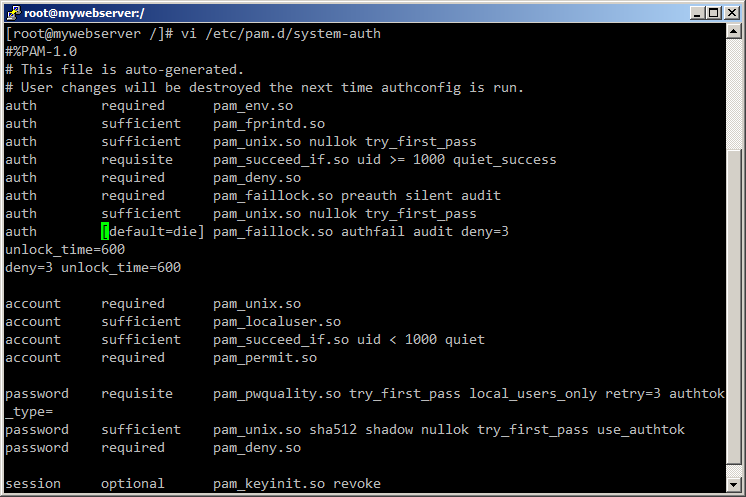
In Red Hat Enterprise Linux 7, the pam_faillock PAM module allows system administrators to lock out user accounts after a specified number of failed attempts.
Limiting user login attempts serves mainly as a security measure that aims to prevent
possible brute force attacks targeted to obtain a user's account password.Follow these steps to configure account locking:
- To lock out any non-root user after three unsuccessful attempts and unlock that user after 10 minutes, add the following lines to the auth section of the /etc/pam.d/system-auth and /etc/pam.d/password-auth files:
auth required pam_faillock.so preauth silent audit
auth sufficient pam_unix.so nullok try_first_pass
auth [default=die] pam_faillock.so authfail audit deny=3
unlock_time=600
deny=3 unlock_time=600 - Add the following line to the account section of both files specified in the previous files:
account required pam_faillock.so
I will show you the end result of one of the files:
Disclaimer - Views expressed in this blog are author's own and do not necessarily represents the policies of aclnz.com
Related Posts